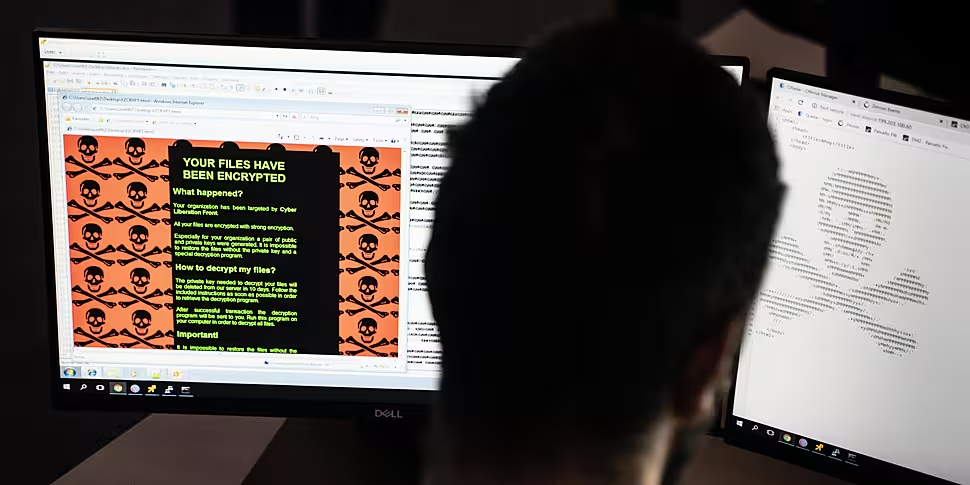
The HSE still needs to overcome a number of challenges to get its systems fully operational after last month's cyber attack, according to a security expert.
The health service has decrypted one-third of its IT servers following the ransomware attack on May 14th.
It is now 30 days since its systems were encrypted by criminals in a ransomware hack and despite a decryption key being provided six days after the incident, there is still widespread disruption to services.
The head of the HSE says the cyber attack will continue to pose extreme risks to many healthcare settings.
Paul Reid, the CEO of the HSE, said that they are still dealing with a “trail of destruction” following the "sophisticated and targeted" attack.
Mr Reid said an estimated 30,000 laptops and 5,000 servers are being replaced as a result of the incident.
Officials from the executive also said they have a better understanding of what may have caused the hack and are finalising a partner to conduct an independent investigation into the attack.
On this week's Tech Talk, Ronan Murphy from SmartTech247 explained to Newstalk's Technology Correspondent Jess Kelly how such ransomware attacks come about.
 File photo. Credit: Eamonn Farrell/RollingNews.ie
File photo. Credit: Eamonn Farrell/RollingNews.ie"I've been in this game for ten years, maybe a little bit longer, and I've never seen anything like the feeding frenzy of ransomware that's currently enveloping the whole world, everywhere from Asia to Europe to North America," he said.
"The scale of it is unprecedented, it feels like a very significant watershed moment in terms of the scale and sheer audacity of what we are witnessing with organisations of all sorts, shapes and sizes right now."
Mr Murphy said that while the attack on the HSE may appear to have come out of nowhere, it shouldn't be too much of a surprise given that similar hacks are having every minute of the day across the globe.
"The blueprint was there, people can say this was a very sophisticated attack and they were blindsided, and they didn't see it coming," he said.
"The truth is, this is happening day in, day out, and there are many examples of them targeting health services across the world.
"These guys are very commercially motivated, they see the health sector as being a low hanging fruit, and therefore they're very aggressively targeting it."
He added that some institutions have legacy systems which make it difficult to constantly update against potential vulnerabilities.
However, even companies with sophisticated security can fall victim to hackers.
 File photo. Credit: Annette Riedl/DPA/PA Images
File photo. Credit: Annette Riedl/DPA/PA Images"If you have out of date systems that arent patched, which is the case in a lot of manufacturing companies and healthcare companies, they're what we term as 'no-touch systems', which means they're not allowed patch them or update them, they're managed by Siemens or GE or someone, so I have a lot of sympathy for organisations that are in that position," he said.
"It is important to note that these attacks do not necessarily target vulnerabilities, I've seen these happen in companies that have the best of equipment implanted and updated.
"Where the problem primarily exists is that organisations will traditionally look at their perimeter - they'll look at their firewalls, they'll look at the stuff that's facing the internet, and they'll try and lock all that down and harden it.
"The issue here is that these guys target individual users, they'll target employees, executives and once they do that, they'll typically do it via email.
"Where the gap arises for organisations is their inability to control what happens inside your network and that's both a mixture of a lack of investment in your cybersecurity tools and monitoring, it's a lack of understanding of how you should architect your network to protect yourself, it's a lack of understanding of the new types of methodologies that are used for hacking."
Mr Murphy said that a scenario where hackers have handed over a decryption key, as happened with the HSE, is something he has never seen before.
"It came from left of field, personally, I think there was pressure on the Russian government, given that we're in a global pandemic it is not good for anyone in any part of the world to have a national health system on its knees and therefore I believe that there was probably some degree of pressure that came from the top down.
"Getting the decryption is not a silver bullet to get back up and running immediately, but it certainly expedites the process and makes it much, much easier.
"I think that's been evidenced, the HSE has a lot of challenges ahead of it still, and it's still trying to get systems operational, but that has significantly improved their situation to get back up and running faster."